Hi,
I’m looking for an instant messaging ( IM ) apps software/protocol that run on Android and computer
and meet the following requirements :
- Open source !
- E2EE
- Messages are send in direct ! (not passing by a server)
- handle group
- Truly private ! ( That’s the tricky part )
The closest that I’ve found is Briar
- +can work without internet ! (bluetooth, local wifi, files !)
- + use TOR
- - Mutual party have to exchange key (or your can introduce someone)
- - sending media suck for now, poor image quality
- - no call or voice messaging
I’ve been looking for alternatives:
Session- Sadly it keep ALL the conversation into server !!! so it’s a no go.
- speek
- I didn’t try it yet, any feedback ?
- simplex
- it look very promising ! (didn’t tried it yet)
- + seem to handle multiple profile in one !
- + do not require that both party send an invitation !
- and have also a optional long term address
! I didn’t found (yet) if the messages are send in direct or pass by a server…
It’s not P2P all the messages pass by servers… too bad.
All post about alternatives or experience with the one that I cited are welcome.
deleted
The “truly private” req really smells with “I have no threat model and don’t know what am I doing”
Yeah. What does privacy mean?
Does it mean nobody knows what you’re saying? Doesn’t mean nobody knows that you’re talking? Doesn’t mean nobody can tell two people have engaged in a conversation?
In addition to direct observations, you can make indirect inferences from many of those characteristics.
If I can observe your peer to peer traffic I know who’s talking to who.
If I can observe your network, onion routing layer, I can determine who is talking to who with high probability
If I can see network traffic at all, I can determine who our members of a group, if the group messages are delivered simultaneously.
is rare, but briar as you identified is pretty good. Though android only.
The trouble with peer to peer is it isn
theres also notification scandal recently which i think the op doesnt know about
Though android only.
Anyway on Windows, Apple there is no sense to have a privacy apps if the OS it self pump everything it can.
And on Android it only make sense if you use an AOSP rom, or another but without the google crapware…
It was always known, in the threat model.
Though I think everyone assumed Google required a warrant.
Even without Google, Apple’s participation and push notifications - signal still has the same capability. Simply because they’ve created a centralized architecture.
If you allow for servers that can’t read your messages (Tor nodes and such), “serverless” messaging is quite possible. All the layers of encryption and redirection aren’t great for latency, but there’s no reason two phones can’t be connected over Tor/Veilid.
The problem in practice, I think, is notifications. To receive notifications, you need to be online all the time. To be available on Tor all the time may help deanonimze you so you also need to shake up your connections every now and then, which requires some CPU heavy recalculations and key exchange from the network as connections are reestablished.
deleted
https://www.privacyguides.org/en/real-time-communication/
https://www.securemessagingapps.com/
Peer to peer messaging is rare, but briar as you identified is pretty good. Though android only.
The trouble with peer to peer is it isn’t very private as the people you message see your connection directly, except with briar
simplex uses relays/servers, but incoming and outgoing messages are configured to pass through separate servers. you can see this in the network settings
Additionally these servers are random per-contact, can be changed around and all data and almost all metadata is either encrypted or otherwise protected ;)
Not exactly what you’re looking for, BUT the best bet would probably be jabber/xmpp. There is a server involved but you can be that server with a ras pi or an old laptop, or VPS, and with OMEMO e2ee, the server can’t see message content only “bob sends X to john.” And as the server owner you can keep no logs and trust yourself.
speek sucks in my opinion , i tried it ,
tbh jami is the best app currently in the p2p messenging space
berty sounds good as well , its built on top of ipfs and weshgaurd
tox is good as well
(i have messaged briar and berty team regarding some questions and i havent gotten its answer , i will update you when i get the answer)
Session doesn’t store logs on a central server. They are encrypted and stored on lokinet.
Anyway other options are: Jami, Signal or Molly and maybe matrix. Keep in mind Briar will drain battery a bit and doesn’t receive notifications offline unless you setup a dedicated device
https://www.securemessagingapps.com/ if you see closely for session , it says that attachments are centralized in their servers in canada
session tries to promote their oxen cryptocurrency and lokinet which imo crypto currency are used by baiters to bait people into ruining their money
you dont understand what signal /molly is , do you ? they are centralized server and OP specificially asked not centralized server / server for that matter
matrix is good but it still need server , plus matrix.org takes quite a bit of metadata
jami’s good but it uses turn server to verify your name
briar’s bluetooth functionality can be violated plus no good ui/ux
Interesting that you mentioned briar and Bluetooth. What is the issue with Bluetooth?
just search seytonic bluetooth on yt , you can find it preety easily ngl
Okay, just on general principles telling me to watch an influencer on YouTube who summarizes an article isn’t a great way to have a discussion.
But whatever, I think this is the article you’re referring to:
https://www.theregister.com/2023/12/06/bluetooth_bug_apple_linux/
Bluetooth keyboard, keystroke injections.
That’s a generalized Bluetooth issue, not a briar issue. I was just curious if there was a specific briar implementation problem, but if this is the article you’re referring to then briar is fine and hasn’t had a issue.
i have an exam tomorrow and as such i wasnt able to show you all the sources
and no currently htrere is no briar specific problem in my radar “yet”
jami’s good but it uses turn server to verify your name
So is it secure ? does that mean you rely on those server to be able to created an account ?
Session does not have centralized servers in Canada. There are issues with session but centralized servers aren’t one of them.
uhh i linked you the website source , no offense but its written there also i hate crypto so maybe thats why i am picking up on those guys specifically i guess
SimpleX uses servers, but they’re just relays and due to SimpleX’s design, no single server can figure out who you are or who you’re talking to. By using Tor they also couldn’t band together and fingerprint you by IP.
If you want to see the model explained, visit their website or just ask here, I’m glad to explain how it keeps your contact graph, identity and messages private :)
A little update.
I’ve just tested simplex on Android.
it’s very well thought out ! The features make sense. UNFORTUNATELY it’s not P2P ! all the messages pass by their servers :'( with Briar it’s P2P… weirdly they claim their way is better than P2P ! any comment on that ?
In my point of view, if messages are stored somewhere it’s mean the can be process[1] !
Cheers.
edit: lemmy link to their community !simplex@lemmy.ml
Copied, analyzed, cracked (Brut force or what ever) ↩︎
It sounds like you’re assuming that everything you put out there isn’t already being stored.
Thank you very much @jet@hackertalks.com & @Quexotic@beehaw.org
The EFF article is really interesting for everyone. ( I was aware of this )
Indeed no one should assume that his packets are not intercepted along the road. But conceive an software that on top of that, specifically route the traffic trough his server not make it better (on the opposite in my opinion)
Even if the owner of those server do not process the data… ( This is relying on blind trust) those servers might be breached. (in addition to the systemic data recording, like in the EFF article )
Let put it simple, is SimpleX offer on the actual Internet (can’t wait the next gen, GNUnet or anything similar) a similar level of Trust & privacy than Briar ?
I’ve did some more digging.
and Briar still remain better at security level !
The big downside of SimpleX is that it’s not P2P and IP correlation by watching your traffic is possible.
SimpleX recommend to use Tor on top of it with for example Orbot. That’s a good idea, but not the best to convince none-tech folks to adopt it. (it’s already so hard to change peoples habit… ) Tor should be embedded.
As soon Tor is embedded I will migrate to it. SimpleX have nice thought features and it’s easy to use.
I don’t know.
Direct peer-to-peer connections giveaway your IP address to the person you’re communicating with. Meaning anybody observing the network can see two people are specifically communicating with each other. Briar attempts to get around this by using Tor to obscure it.
But briar is using Tor as a relay, just like simple x does. The architectures are very similar from that lens.
To your threat model, ideally data does not rest on the network, but you have to assume any data that hits the network is being recorded by a bad actor to be analyzed later.
It’s been stuck in “coming soon” hell for ages, but VeilidChat may be of interest to you.
TorChat is rather clunky, but any privacy respecting chat app without an intermediate server will be. Is a bit like Tor but with some improvements, so running a chat protocol on top of it should work better.
Note that there is an app called “veilid chat” out there that doesn’t seem to have anything to do with the people writing code on the Veilid network.
Thanks for the sharing @skullgiver@popplesburger.hilciferous.nl
I’ve check
VeilidChatfor the moment indeed it is just a network framework… so no apps ready yet (unless I’m mistaken )The negative point is that the developer use exclusively google tech for it !! ( Dart, flutter )
So why peoples that want to fight for freedom use the Sauron tool !? it baffle me…
Meahtastic and LoRa actually meet your requirements
https://www.youtube.com/watch?v=EAQI2ZSmxPU
Peer to peer messaging, line of sight.
Have you looked in to Jami?
no ! thanks ! look promising too.
I’ll try it and give my review… but is it require to make a “jami” account on their server !??
As I understand it, the account is on your machine only. If you delete your profile, it’s gone, unless you made backups. But I may be mistaken.
I think your mistaken… Can someone confirm ?
So I was eager to test Jami, but on Windows it require Windows 10… so no way --> https://itvision.altervista.org/why-windows-10-sucks.html
anyway I gave a quick try on a test machine (win10) But I got , not matter what I entered
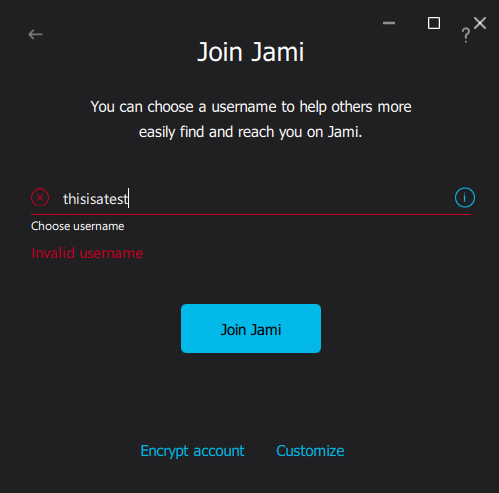
Too bad because it had on paper, a lot of nice features…
On linux, too bad they don’t provide (yet) an AppImage…






